Top 5 Cybersecurity Threats in Nigeria: Protect Your Digital Life

In today’s digital age, cybersecurity threats are becoming increasingly sophisticated, posing significant risks to individuals, businesses, and organizations in Nigeria. As the country continues to grow digitally, it’s essential to stay informed about the most prevalent threats and take proactive measures to protect yourself. In this article, we’ll explore the top 5 cybersecurity threats in […]
5 FREE PARENTAL CONTROL APPS-EASY TO USE

When it comes to keeping your child safe in the digital space, parental control apps can be a valuable tool. They offer various features to help manage screen time, monitor online activity, and block inappropriate content. Here are some of the best parental control apps available: 1. Google Family Link Features: Screen time management, app activity monitoring, […]
Protecting Your Child in the Digital Space: A Parent’s Guide

In today’s digital age, our children are growing up in a world that’s vastly different from the one we knew. The internet is an incredible resource, offering endless opportunities for learning, creativity, and connection. However, it also presents new challenges and risks that parents need to navigate. As digital guardians, it’s crucial to understand how […]
Protect Your Online Identity: Why Signing In with Facebook or Google is not a good idea
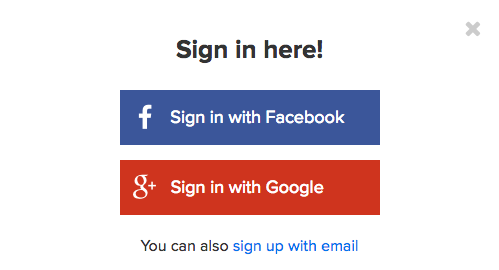
While signing in with Facebook or Google might seem convenient, it can compromise your online security and privacy. KEYNOTES You’re giving Facebook or Google control over your account, which means they can lock you out at any time. These companies collect and share your data with third-party apps and sites, putting your privacy at risk. […]
A Guide to Cloud Storage Security

Imagine a magic vault where you can stash all your favorite photos, documents, and videos. Sounds cool, right? That’s basically what cloud storage is – a secure online space to store your digital treasures. But, just like a real vault, you want to make sure it’s locked tight and only you have the key. That’s […]
The Importance of Home Security in Today’s World

Home security is a critical concern for homeowners, as it provides protection and peace of mind. In today’s world, home security is more important than ever, due to: – Increased crime rates – Advanced technology and smart homes – Growing concern for family safety By investing in a comprehensive home security system, homeowners can protect […]

